Why Image Analysis is Used in Modernized Check Fraud Detection
Post Summary
- Specific problematic use cases
- Check fraud has evolved
- Using independent data sources improves fraud predictions
Multivariate analysis addresses gaps in legacy, transactional analytics
As a payment professional, you know the nuances differentiating a check and an ACH or Zelle payment. When considering fraud detection and prevention on these payments, it makes sense to optimize an approach for each payment type.
Or does it?
Checks have a unique set of fraud scenarios which need to be considered. For example:
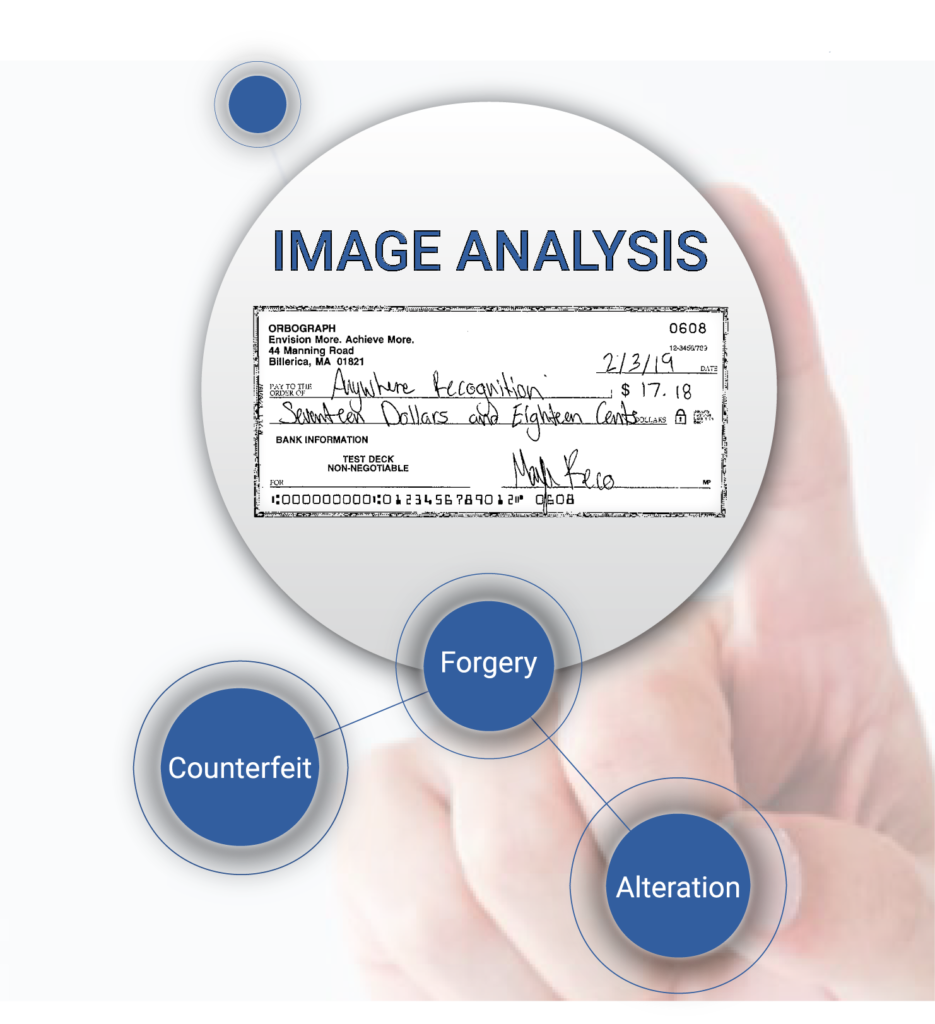
- There are several main check fraud categories:
– Counterfeits: These are fake checks and there are many ways to create them.
– Forgeries: Unauthorized or forged signatures occur on stolen or modified checks.
– Alteration: Changing the dollar amount or payee or other fields of an item.
– Kiting: Still used with limited “float”, fraudsters take different approaches now, often incorporating electronic transactions into the mix. - Banks must factor the above categories with loss management. Are you the Bank of First Deposit (BoFD) or the paying bank? A fraud liability can rest on whether you have strong controls on the right workflow.
- Fraud return windows: Time zones and regulatory processing time-frames dictate where the risk of fraud loss falls.
- Unlike electronic payments, fields like payee, payor, date, etc. are printed or written on the check, whereas electronic payments are inherently “electronic.”
Because of the unique attributes of checks, there are many fraudulent use cases which are difficult to detect. Let’s look at how banks are trying to address these problems.
Transaction Analysis Evolution in Check
Check fraud detection started with the manual review of items which were out-sorted from reader sorters (remember reader sorters?). Then, basic analytics were developed to analyze MICR data (amounts, serial numbers, velocity) for transactional analysis. Does ASI-16 and ASI-19 ring a bell? Although it’s 20-30 year old technology, many banks still use “legacy analytics” within their enterprise fraud solutions.
Today, fraud detection and prevention is heading toward real-time. This has brought a new wave of vendors to the table. The legacy transaction analysis fraud vendors are trying to adapt, and while they do provide a baseline of protection, these solutions cannot stay ahead of fraudsters. This results in detection gaps.
These use case examples illustrate new potential gaps to close in detection:
- Mobile RDC has revolutionized capture. This is now a new entry point for fraud.
- EMV tightened up protections to credit card. Fraudsters returned to find weak points in legacy check protection systems.
- Customer convenience and improved funds availability is both a blessing and a curse. Omnichannel capture/deposit of checks means that fraudsters can deposit money and have access by next morning.
To address these cases, many banks developed their own transactional analysis and even kicked off AI and machine learning initiatives. The Hewlett Packard Enterprise report shows strategically how AI and ML fit into the picture.
In fact, here’s how AI is being deployed:
In December of 2018, Citi announced plans to integrate Feedzai’s ML-driven transaction management monitoring system into its own proprietary services and platforms, with the aim of providing business customers with enhanced risk management for payment transactions.
Image Analysis: True Multivariate Analysis
So, with all these improvements going on in the industry, why are 20+ banks issuing RFPs and requesting information for modernized image analysis technologies?
- Layman’s answer: The strength of image analysis resides in the ability to “see the attributes of an image” and compare that to previously cleared checks for match purposes. This can only be done via image processing software or by the human eye.
- Technical answer: Multivariate analysis measures two or more independent variables (Xi) simultaneously to predict a value of a dependent variable (Y) for each subject. Images are ignored in basic transaction analytics and machine learning.
For example, many times the perpetrator is using a different check stock for a counterfeit, forgers use unauthorized signatures, and alterations can only be seen on the image. Transactional-only systems will analyze data fields and are unable to defects in the image. The image analysis tests (check stock validation, amount verification, automated signature verification, and check style validation) are the independent variables combined with the transactional data which drives up detection and reduces false positives. The potential loss savings is in the millions of dollars for many banks.
For more details on image analysis analyzers, review the Anywhere Fraud feature page.