Fraud Scheme — Straight from the Movies?
- An employee used his access to software and accounts to steal money
- His inspiration came from the film OFFICE SPACE
- This scam was not his only scheme
Movies can inspire many behaviors, both good and bad. For decades many bartenders, for instance, have been subjected to the request that a drink be "shaken, not stirred" because the customer is fresh from a James Bond marathon.
The Washington Post tells the story of a movie-emulator who instigated a copy-cat crime inspired by the 1990 film Office Space. Ermenildo “Ernie” Castro, a 28 year-old software engineer, followed the diabolical example he saw in the film:
And so the software engineer, much like the disaffected tech workers in the 1999 cult classic, allegedly injected malicious computer code into his employer’s information-technology system. For months, that code rerouted a portion of the shipping charges on tens of thousands of customers’ purchases, sending money to an account controlled by Castro instead of the online retailer he worked for, Seattle police wrote in court documents.

Understanding the Fraud Scheme
Castro was certainly in the right position to pull off such a crime. The Post reports that he began work at the company in 2018, and his position as a software engineer on the “Shopping Experience” team meant he wrote computer code to improve the checkout process on the company’s website, a Seattle Police Department detective wrote in an affidavit.
Then, at the end of February, Castro changed the code to enrich himself, the affidavit states: When tens of thousands of sales were made, shipping fees were sent to an account he personally controlled. That scheme, which affected “a small percentage of Zulily customer check-outs,” netted him over $110,000, according to court documents.

After investigators began to notice the leak, Castro attempted to "backpedal" and replace the funds by writing code that charged customers double the normal shipping costs, sending half to Zulily and half to his own account.
After getting fired, Castro returned his company laptop. As part of its investigation, Zulily copied and analyzed the contents of the hard drive, ultimately relaying its findings to law enforcement.
Steve Carney, the company’s director of cybersecurity, reported that he’d found a document on the laptop titled “OfficeSpace project,” which allegedly laid out the scheme to steal the shipping fees. (In the movie, employees infect their company’s accounting system with a virus meant to repeatedly divert fractions of a cent into a bank account they’ve set up.)
This was not Castro's only misadventure.
Meanwhile, Castro was allegedly working another con. On May 27, he started emailing a woman he would later say he’d met on the dating app Tinder and had been seeing for a month, the affidavit states. In the emails, police say, the woman sent Castro links to online shopping carts filled with Zulily merchandise she wanted. Castro allegedly replied to confirm he’d purchased the items she’d identified in what police described as “a ‘wish list’ of sorts.”
But he was cutting prices so he could buy them for pennies on the dollar, the affidavit states. Overall, he paid about $254 for nearly 1,300 items worth more than $41,000, according to the affidavit.
Unfortunately, recovery of the stolen funds will take a while.
“He clarified that he had used the money to invest in stock options, particularly GameStop stock options,” the detective said in the affidavit, “and reiterated that all the money was now gone.”
Insider Fraud Schemes are NOT Uncommon
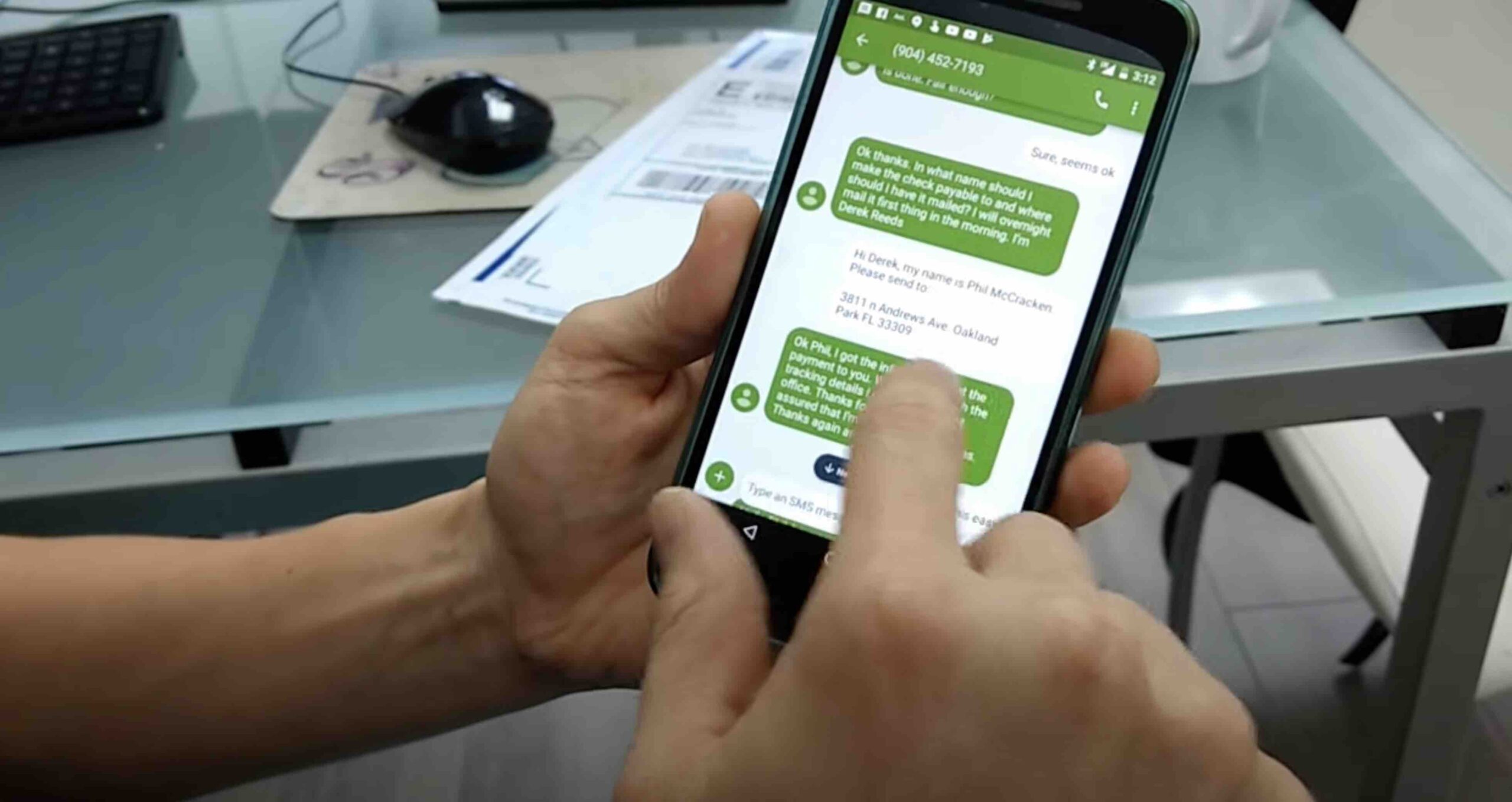
Business are vulnerable to insider fraud schemes and embezzlement -- particularly when poor controls are in place. While Castro's fraud scheme is more sophisticated with coding, there are hundreds of thousands of cases every year of employees stealing funds from their employers -- particularly when it comes to checks.
Heck, even successful billionaires like Mark Cuban have been the victim:
And we all know about the stolen mail epidemic currently plaguing the US Post Office. Just like any other business, they are not immune to employees stealing.
For businesses, positive pay systems are the most effective solution when it comes to stolen company checks. With the integration of AI and machine learning technology that accurately reads the payee name -- detecting alterations by both reading the payee as well as searching for payee replacements and payee edits, including “and/or” additions to the printed payee field -- and comparing it to the payee issue file source, fraudulent payments can be stopped before the funds are extracted.